In today’s rapidly evolving digital landscape, organizations face a growing number of cybersecurity challenges. From sophisticated cyberattacks to internal system weaknesses, the need to proactively identify and mitigate risks has never been greater. Two essential components of any strong security strategy are risk assessment and vulnerability assessment. While these terms are often used interchangeably, they serve distinct purposes and play unique roles in safeguarding systems and data.
Understanding the relationship between risk, threat, and vulnerability, as well as the difference between risk vs vulnerability, is crucial for building an effective cybersecurity framework. This article explores the key insights and differences between risk assessment and vulnerability assessment, helping organizations make informed decisions about their security posture.
Understanding the Basics: Risk, Threat, and Vulnerability
Before diving into comparisons, it’s important to clarify three foundational concepts: risk, threat, and vulnerability.
- Threat: A threat is any potential event or action that could cause harm to a system or organization. This could include hackers, malware, insider threats, or even natural disasters.
- Vulnerability: A vulnerability is a weakness or flaw in a system, network, or process that can be exploited by a threat.
- Risk: Risk is the potential for loss or damage when a threat exploits a vulnerability. It is often calculated based on the likelihood of an event occurring and its potential impact.
In simple terms:
Risk = Threat × Vulnerability × Impact
This relationship highlights why both risk assessment and vulnerability assessment are critical—they address different parts of the same equation.
What is a Vulnerability Assessment?
A vulnerability assessment is a systematic process used to identify, classify, and prioritize security weaknesses in systems, networks, or applications. Its primary focus is on discovering technical flaws that could be exploited by attackers.
Key Characteristics
- Identifies known vulnerabilities (e.g., outdated software, misconfigurations)
- Uses automated tools and scanners
- Provides a list of weaknesses ranked by severity
- Focuses on “what is broken” in the system
Common Types of Vulnerabilities
- Unpatched software
- Weak passwords
- Misconfigured firewalls
- Open ports and services
- Outdated encryption protocols
Benefits of Vulnerability Assessment
- Helps organizations detect security gaps early
- Improves system hardening
- Supports compliance requirements
- Provides actionable remediation steps
However, vulnerability assessments do not consider the broader business context or the likelihood of exploitation. This is where risk assessment comes in.
What is a Risk Assessment?
A risk assessment goes beyond identifying vulnerabilities. It evaluates the potential impact and likelihood of threats exploiting those vulnerabilities, helping organizations prioritize what truly matters.
Key Characteristics
- Focuses on business impact and likelihood
- Considers threats, vulnerabilities, and consequences
- Involves both technical and non-technical factors
- Provides risk levels (low, medium, high, critical)
Components of Risk Assessment
- Asset Identification
Identifying critical systems, data, and resources. - Threat Analysis
Understanding potential sources of harm. - Vulnerability Evaluation
Reviewing weaknesses that could be exploited. - Impact Assessment
Determining the potential damage if an incident occurs. - Likelihood Determination
Estimating how probable the event is.
Benefits of Risk Assessment
- Aligns security efforts with business priorities
- Enables better decision-making
- Helps allocate resources effectively
- Reduces overall organizational risk
Unlike vulnerability assessments, risk assessments provide a strategic, big-picture view.
Risk vs Vulnerability: Key Differences
Understanding risk vs vulnerability is essential for distinguishing between these two processes. While they are closely related, they are not the same.
| Aspect | Vulnerability Assessment | Risk Assessment |
| Focus | Identifying weaknesses | Evaluating potential impact |
| Scope | Technical issues | Business + technical context |
| Output | List of vulnerabilities | Risk levels and priorities |
| Approach | Automated tools | Analytical and contextual |
| Goal | Fix weaknesses | Manage and reduce risk |
How Risk and Vulnerability Assessments Work Together
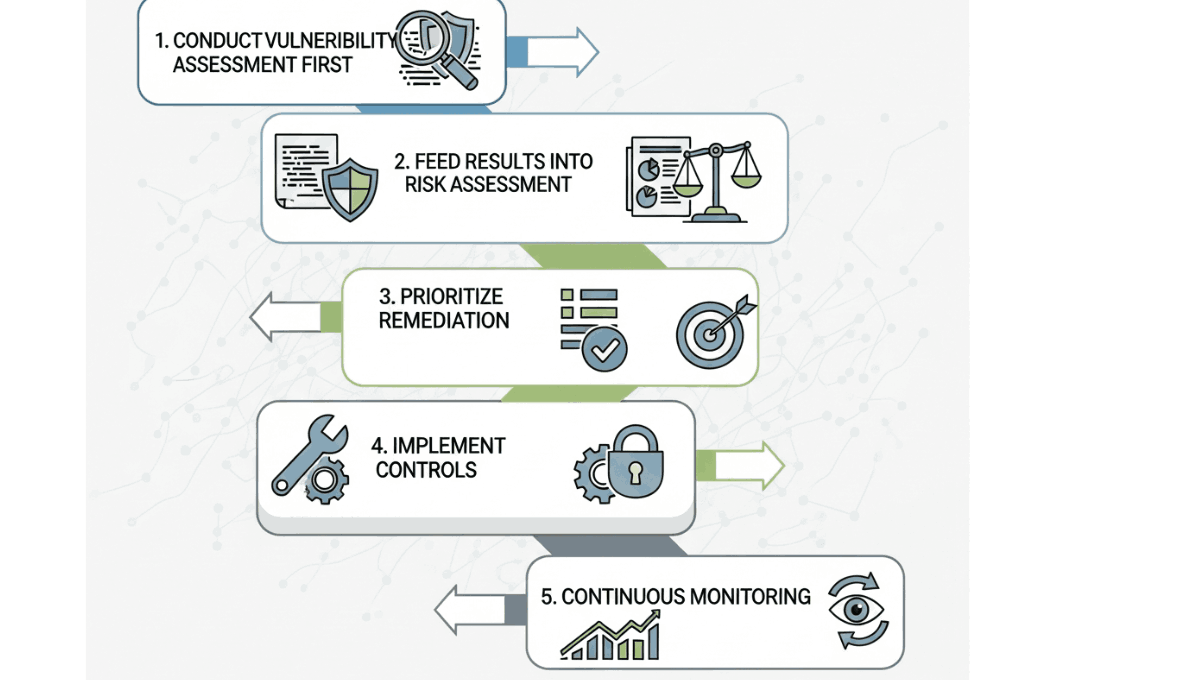
Rather than choosing between them, organizations should use both assessments as complementary processes.
Step-by-Step Integration
- Conduct Vulnerability Assessment First
Identify all possible weaknesses in your systems. - Feed Results into Risk Assessment
Evaluate which vulnerabilities pose the greatest risk. - Prioritize Remediation
Focus on vulnerabilities that have high risk scores. - Implement Controls
Apply patches, security measures, and policies. - Continuous Monitoring
Repeat assessments regularly to stay protected.
This combined approach ensures that organizations are not just fixing issues blindly but are addressing the most critical risks first.
Tools and Techniques
Vulnerability Assessment Tools
- Network scanners
- Web application scanners
- Configuration auditing tools
These tools automate the process of finding vulnerabilities quickly and efficiently.
Risk Assessment Methods
- Qualitative analysis (low, medium, high)
- Quantitative analysis (numerical scoring)
- Framework-based approaches (like ISO, NIST)
Risk assessments often involve human judgment and business understanding, making them more complex but also more valuable.
Challenges in Implementation
Vulnerability Assessment Challenges
- False positives
- Large volumes of data
- Requires frequent updates
Risk Assessment Challenges
- Subjectivity in scoring
- Time-consuming process
- Requires cross-department collaboration
Organizations must balance automation with human expertise to overcome these challenges.
Best Practices
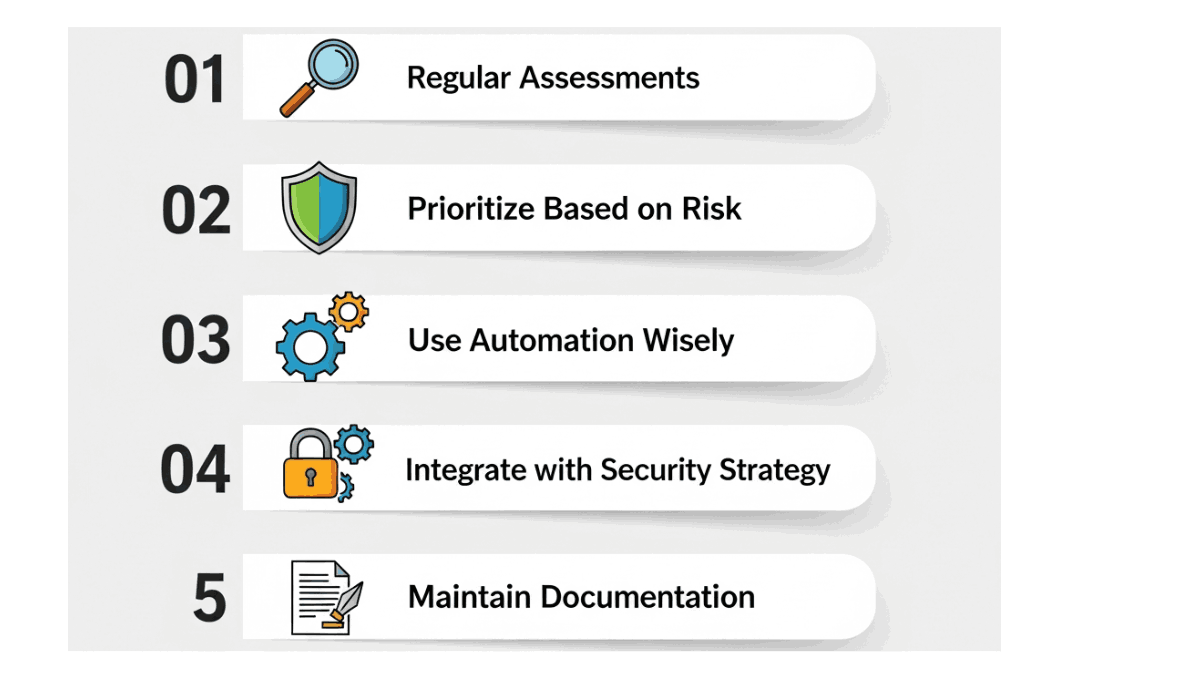
To maximize the effectiveness of both assessments, consider the following best practices:
1. Regular Assessments
Conduct vulnerability scans and risk assessments periodically to keep up with evolving threats.
2. Prioritize Based on Risk
Not all vulnerabilities are equal—focus on those with the highest risk.
3. Use Automation Wisely
Automate vulnerability detection but apply human analysis for risk evaluation.
4. Integrate with Security Strategy
Align assessments with overall cybersecurity goals and business objectives.
5. Maintain Documentation
Keep records of findings, decisions, and remediation efforts for compliance and improvement.
Why Both Are Essential
In the debate of risk vs vulnerability, the truth is that both are indispensable. Vulnerability assessments provide the raw data, while risk assessments provide the context needed to act on that data effectively.
Without vulnerability assessment:
- You don’t know where your weaknesses are
Without risk assessment:
- You don’t know which weaknesses matter most
Together, they form the backbone of a robust cybersecurity strategy.
Conclusion
Understanding the difference between risk assessment and vulnerability assessment is critical for any organization aiming to strengthen its security posture. While vulnerability assessments focus on identifying weaknesses, risk assessments evaluate the potential impact and likelihood of those weaknesses being exploited.
By clearly understanding risk, threat, and vulnerability, and applying both assessment methods in tandem, organizations can move from reactive security to proactive risk management. The key is not to choose one over the other, but to integrate both into a continuous, strategic process.
In an era where cyber threats are constantly evolving, this combined approach ensures that resources are used efficiently, risks are minimized, and critical assets remain protected.
Ultimately, mastering the balance between vulnerability detection and risk evaluation is what separates a basic security setup from a truly resilient cybersecurity framework.